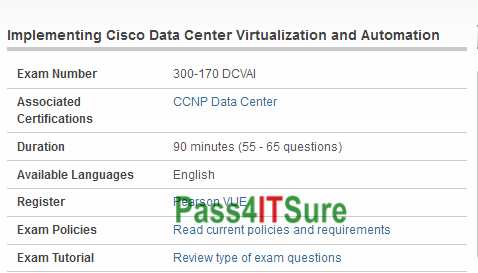
What are the best study tools for the Cisco 300-170 dumps? The DCVAI Implementing Cisco Data Center Virtualization and Automation (DCVAI) (300-170 DCVAI) exam is a 90 minutes (55 – 65 questions) assessment in pass4itsure that is associated with the CCNP Data Center certification. High quality Cisco 300-170 dumps DCVAI exam practice test with new discount Youtube training. “DCVAI Implementing Cisco Data Center Virtualization and Automation (DCVAI)” is the exam name of Pass4itsure Cisco 300-170 dumps test which designed to help candidates prepare for and pass the Cisco 300-170 exam. The achievement of Implementing Cisco Data Center Virtualization and Automation validates that the candidate monitors the on a regular basis against all the possible threats and vulnerabilities with the help of knowledge, tools, and concepts. Earning https://www.pass4itsure.com/300-170.html dumps Implementing Cisco Data Center Virtualization and Automation is so beneficial security administrators, Data Networking.
[100% Valid Cisco 300-170 Dumps Questions]: https://drive.google.com/open?id=0BwxjZr-ZDwwWZzkydEcwa19TQWM
[100% Valid Cisco 300-175 Dumps Questions]: https://drive.google.com/open?id=0BwxjZr-ZDwwWUUZ4UURySG9IdE0
Pass4itsure Free Cisco 300-170 Dumps Exam Questions and Answers:
QUESTION 8 You work as a buyer at KillTest .com. A piece of capital equipment is designed and specified so as to force the purchasing department into a sole supplier situation. You still want to affect the procurement process. Which of the following support items from the sole supplier would you negotiate? (Choose all that apply)
A. Technical documentation, including data sheets, performance specs, maintenance and operating manuals, supplier-furnished training programs, and full supplier documentation
B. The initial provisioning of high-risk spare parts for start-up and a one-year period thereafter
C. A promise to maintain equipment on an annual basis by the manufacturer or its authorized service agent
D. A determination of whether equipment or services are taxable or tax-exempt
300-170 exam Answer: A, B, C
QUESTION 9 Which of the following phrases are used to refer to the receipt of a functional acknowledgment after sending a purchase order via EDI?
A. transmission received B. accepted purchase order
C. valid contract exists D. goods have been shipped
Answer: A
QUESTION 10 With which of the following would purchasing management be MOST concerned in day-to-day operational control in a manufacturing firm?
A. labor utilization variance
B. materials utilization variance
C. labor cost variance
D. materials cost variance
300-170 dumps Answer: D
QUESTION 11 Which of the following tools are MOST important for achieving continuous improvements in an organization’s integration with its supplier?
A. Quality inspection at the plant B.
Involvement in product design C.
Suppliers input in forms design
D. Joint examination of costs structure
Answer: B
QUESTION 12 Which of the following terms is NOT associated with the Internet?
A. Browsers
B. Home pages
C. Web sites
D. Time sharing
300-170 pdf Answer: D
QUESTION 13 Which statement about setting negotiating objectives is FALSE?
A. It should be defined with sufficient specificity to permit measurements.
B. It should be established for each issue or condition to be negotiated.
C. They should establish a supplier’s strengths and avoid reference to its weaknesses.
D. It should be based on databases derived from cooperative efforts of purchasing,
production, and engineering.
Answer: C
QUESTION 14 If a supplier’s level of quality was unsatisfactory on past orders and the level of quality on current orders is critical, which of the following options would be the BEST way to handle the situation?
A. Timely inspection by the buyer’s company at the supplier’s plant
B. Requiring the supplier to supply extra products to cover rejects
C. Require 100% inspection before the products leave the warehouse of the order by the buyer’s company’s quality control department
D. Label “Quality of Material is Critical” on the purchase order
300-170 vce Answer: A
QUESTION 15 If a manufacturer establishes all the population needed for a round-bar machining process being 5.76 centimeters, with a standard deviation of 15. The acceptable quality limits are estimated at about 3 standard deviations. On day one, the sample means are taken by the operator, 5.80, 5.46, and 6.20 centimeters. These means indicate if the process is
A. controlled
B. reckless
C. statistically perfect
D. leaning towards the lower side of the mean
Answer: A
QUESTION 16 Which of the following factors are causing growth in complexity of much procurements leading to an increased trend towards:
A. suppliers partnering
B. cross-functional teams
C. risk factor management
D. strategic supplier alliances
300-170 exam Answer: B
QUESTION 17 Which of the following options are key actions that senior management should take into account when establishing a purchasing department?
A. Select a purchasing system
B. Develop list of suppliers
C. Hire qualified buyers
D. Establish a policies authorizing purchasing authority
Answer: D
QUESTION 18
Which of the following situations must be corrected FIRST to ensure successful information security governance within an organization?
A. The information security department has difficulty filling vacancies.
B. The chief information officer (CIO) approves security policy changes.
C. The information security oversight committee only meets quarterly.
D. The data center manager has final signoff on all security projects.
300-170 dumps Correct Answer: D
Explanation
Explanation/Reference:
Explanation:
A steering committee should be in place to approve all security projects. The fact that the data center manager has final signoff for all security projects indicates that a steering committee is not being used and that information security is relegated to a subordinate place in the organization. This would indicate a failure of information security governance. It is not inappropriate for an oversight or steering committee to meet quarterly. Similarly, it may be desirable to have the chief information officer (CIO) approve the security policy due to the size of the organization and frequency of updates. Difficulty in filling vacancies is not uncommon due to the shortage of good, qualified information security professionals.
QUESTION 19
Which of the following requirements would have the lowest level of priority in information security?
A. Technical
B. Regulatory
C. Privacy
D. Business
Correct Answer: A
Explanation
Explanation/Reference:
Explanation:
Information security priorities may, at times, override technical specifications, which then must be rewritten to conform to minimum security standards. Regulatory and privacy requirements are government mandated and, therefore, not subject to override. The needs of the business should always take precedence in deciding information security priorities.
QUESTION 20
When an organization hires a new information security manager, which of the following goals should this individual pursue FIRST?
A. Develop a security architecture
B. Establish good communication with steering committee members
C. Assemble an experienced staff
D. Benchmark peer organizations
300-170 pdf Correct Answer: B
Explanation
Explanation/Reference:
Explanation:
New information security managers should seek to build rapport and establish lines of communication with senior management to enlist their support. Benchmarking peer organizations is beneficial to better understand industry best practices, but it is secondary to obtaining senior management support. Similarly, developing a security architecture and assembling an experienced staff are objectives that can be obtained later.
QUESTION 21
It is MOST important that information security architecture be aligned with which of the following?
A. Industry best practices
B. Information technology plans
C. Information security best practices
D. Business objectives and goals
Correct Answer: D
Explanation
Explanation/Reference:
Explanation:
Information security architecture should always be properly aligned with business goals and objectives. Alignment with IT plans or industry and security best practices is secondary by comparison.
QUESTION 22
Which of the following is MOST likely to be discretionary?
A. Policies
B. Procedures
C. Guidelines
D. Standards
300-170 vce Correct Answer: C
Explanation
Explanation/Reference:
Explanation:
Policies define security goals and expectations for an organization. These are defined in more specific terms within standards and procedures. Standards establish what is to be done while procedures describe how it is to be done. Guidelines provide recommendations that business management must consider in developing practices within their areas of control; as such, they are discretionary.
QUESTION 23
Security technologies should be selected PRIMARILY on the basis of their:
A. ability to mitigate business risks.
B. evaluations in trade publications.
C. use of new and emerging technologies.
D. benefits in comparison to their costs.
Correct Answer: A
Explanation
Explanation/Reference:
Explanation:
The most fundamental evaluation criterion for the appropriate selection of any security technology is its ability to reduce or eliminate business risks. Investments in security technologies should be based on their overall value in relation to their cost; the value can be demonstrated in terms of risk mitigation. This should take precedence over whether they use new or exotic technologies or how they are evaluated in trade publications.
QUESTION 24
Which of the following are seldom changed in response to technological changes?
A. Standards
B. Procedures
C. Policies
D. Guidelines
300-170 exam Correct Answer: C
Explanation
Explanation/Reference:
Explanation:
Policies are high-level statements of objectives. Because of their high-level nature and statement of broad operating principles, they are less subject to periodic change. Security standards and procedures as well as guidelines must be revised and updated based on the impact of technology changes.
QUESTION 25
The MOST important factor in planning for the long-term retention of electronically stored business records is to take into account potential changes in:
A. storage capacity and shelf life.
B. regulatory and legal requirements.
C. business strategy and direction.
D. application systems and media.
Correct Answer: D
Explanation
Explanation/Reference:
Explanation:
Long-term retention of business records may be severely impacted by changes in application systems and media. For example, data stored in nonstandard formats that can only be read and interpreted by previously decommissioned applications may be difficult, if not impossible, to recover. Business strategy and direction do not generally apply, nor do legal and regulatory requirements. Storage capacity and shelf life are important but secondary issues.
QUESTION 26
Which of the following is characteristic of decentralized information security management across a geographically dispersed organization?
A. More uniformity in quality of service
B. Better adherence to policies
C. Better alignment to business unit needs
D. More savings in total operating costs
300-170 dumps Correct Answer: C
Explanation
Explanation/Reference:
Explanation:
Decentralization of information security management generally results in better alignment to business unit needs. It is generally more expensive to administer due to the lack of economies of scale. Uniformity in quality of service tends to vary from unit to unit.
QUESTION 27
Which of the following is the MOST appropriate position to sponsor the design and implementation of a new security infrastructure in a large global enterprise?
A. Chief security officer (CSO)
B. Chief operating officer (COO)
C. Chief privacy officer (CPO)
D. Chief legal counsel (CLC)
Correct Answer: B
Explanation
Explanation/Reference:
Explanation:
The chief operating officer (COO) is most knowledgeable of business operations and objectives. The chief privacy officer (CPO) and the chief legal counsel (CLC) may not have the knowledge of the day- to-day business operations to ensure proper guidance, although they have the same influence within the organization as the COO. Although the chief security officer (CSO) is knowledgeable of what is needed, the sponsor for this task should be someone with far-reaching influence across the organization.
QUESTION 28
Which of the following would be the MOST important goal of an information security governance program?
A. Review of internal control mechanisms
B. Effective involvement in business decision making
C. Total elimination of risk factors
D. Ensuring trust in data
300-170 pdf Correct Answer: D
Explanation
Explanation/Reference:
Explanation:
The development of trust in the integrity of information among stakeholders should be the primary goal of information security governance. Review of internal control mechanisms relates more to auditing, while the total elimination of risk factors is not practical or possible. Proactive involvement in business decision making implies that security needs dictate business needs when, in fact, just the opposite is true. Involvement in decision making is important only to ensure business data integrity so that data can be trusted.
QUESTION 29
Relationships among security technologies are BEST defined through which of the following?
A. Security metrics
B. Network topology
C. Security architecture
D. Process improvement models
Correct Answer: C
Explanation
Explanation/Reference:
Explanation:
Security architecture explains the use and relationships of security mechanisms. Security metrics measure improvement within the security practice but do not explain the use and relationships of security technologies. Process improvement models and network topology diagrams also do not describe the use and relationships of these technologies.
“DCVAI Implementing Cisco Data Center Virtualization and Automation (DCVAI)”, also known as 300-170 exam, is a Cisco certification which covers all the knowledge points of the real Cisco exam. Pass4itsure Cisco 300-170 dumps exam questions answers are updated (102 Q&As) are verified by experts. The associated certifications of 300-170 dumps is CCNP Data Center. Cisco https://www.pass4itsure.com/300-170.html dumps Cisco Certified Network Professional Data Center is one of the best multifaceted certificates to help you enter the Implementing Cisco Data Center Virtualization and Automation career to advance your existing IT role with the advanced skills in demand.